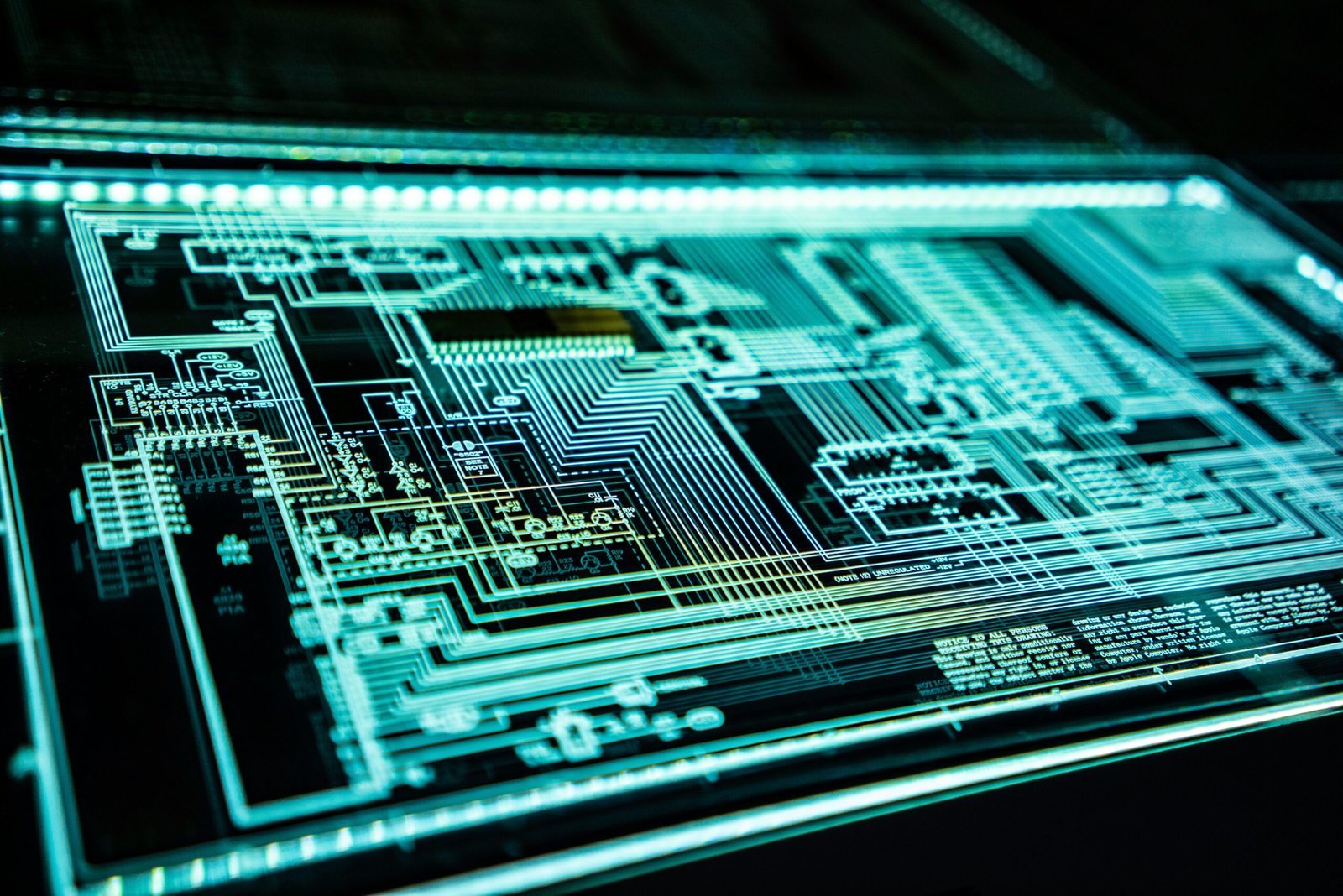
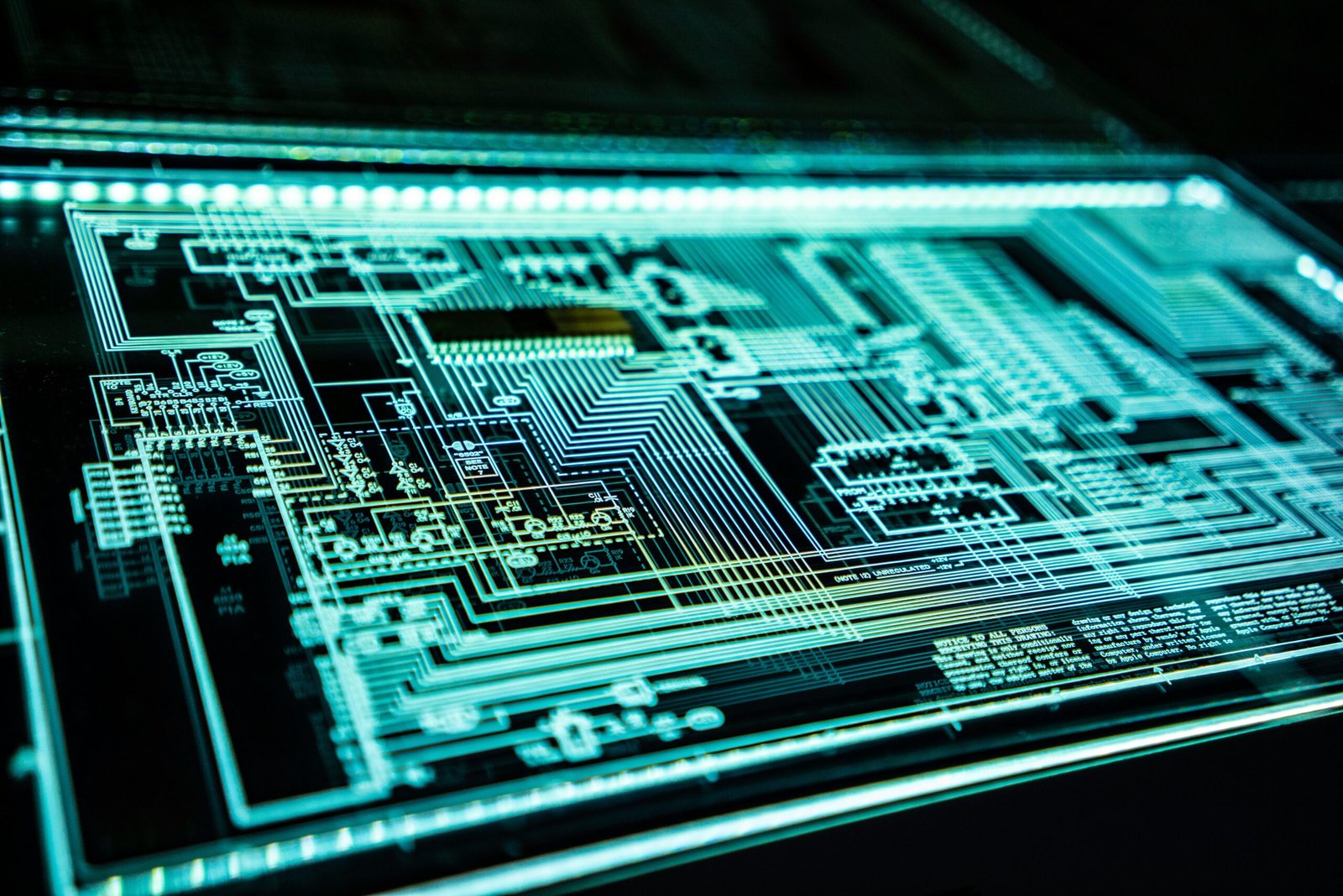
Introduction: The Digital Age and Its Perils
The advent of the digital age has revolutionized the way we live, work, and interact. With rapid advancements in technology, the internet has become an indispensable part of our daily lives, facilitating everything from communication and entertainment to commerce and education. This unprecedented connectivity offers unparalleled convenience, enabling us to access information, services, and each other with just a few clicks. However, this progress comes with a dual-edged nature, presenting significant challenges to information security and privacy.
As we increasingly rely on the internet, the volume of personal and sensitive data circulating online has soared. From social media profiles to financial transactions, a vast array of information is continuously shared and stored across numerous platforms. While this data exchange enhances our digital experiences, it also exposes us to a myriad of risks. Cyber threats such as hacking, phishing, and data breaches have become more sophisticated and prevalent, posing serious dangers to individuals and organizations alike.
The rise of cybercrime is a stark reminder of the vulnerabilities inherent in our interconnected world. Malicious actors exploit weaknesses in systems and networks to gain unauthorized access to valuable information, leading to identity theft, financial loss, and reputational damage. Moreover, the pervasive collection and analysis of user data by corporations raise significant privacy concerns. The potential for misuse of this information, whether for targeted advertising, surveillance, or other purposes, underscores the need for robust information security measures.
In this context, ensuring the security and privacy of our digital lives has become a paramount concern. The evolving landscape of cyber threats necessitates continuous vigilance and proactive strategies to protect sensitive information. This blog post aims to delve deeper into the intricate challenges we face in safeguarding our data in the digital age, exploring the complexities and potential solutions to this pressing issue.
Understanding Information Security and Privacy
In the digital age, understanding the nuances between information security and privacy is paramount. Information security refers to the practices and protocols designed to protect data from unauthorized access, use, disclosure, disruption, modification, or destruction. This encompasses a wide range of techniques and tools, such as encryption, firewalls, and intrusion detection systems, aimed at safeguarding data integrity and availability.
Privacy, on the other hand, is centered around the protection of personal data from being misused or improperly shared. It involves ensuring that personal identifiable information (PII) — such as names, addresses, social security numbers, and other sensitive data — is handled responsibly and with consent. The objective of privacy is to provide individuals with control over their personal information and to prevent unauthorized parties from accessing or exploiting it.
To delve deeper, encryption is a critical concept in both information security and privacy. It involves converting data into a coded format that can only be accessed with a decryption key, thereby ensuring that even if data is intercepted, it remains unreadable to unauthorized users. Data breaches, another key term, refer to incidents where sensitive, protected, or confidential data is accessed or disclosed in an unauthorized manner, posing severe risks to both information security and privacy.
Personal Identifiable Information (PII) is a term frequently encountered in discussions of privacy. PII includes any data that can be used to identify, contact, or locate an individual, such as email addresses, phone numbers, and biometric records. Protecting PII is crucial as its misuse can lead to identity theft, financial loss, and other personal harms.
Understanding the distinction and interplay between information security and privacy is essential for developing robust strategies to protect data in today’s interconnected world. By prioritizing both, organizations can not only safeguard their data assets but also build trust with users by ensuring their personal information is handled with the utmost care and respect.
Common Threats to Information Security and Privacy
The digital landscape is fraught with various threats that pose significant risks to information security and privacy. Understanding these threats is crucial in safeguarding personal and organizational data. Among the most prevalent threats are malware, phishing attacks, ransomware, social engineering, man-in-the-middle attacks, and insider threats. Each of these has distinct characteristics and methods of compromising sensitive information.
Malware refers to malicious software designed to infiltrate and damage computer systems. This category includes viruses, worms, Trojans, and spyware. Malware can steal sensitive information, corrupt files, and render systems inoperable. It often spreads through email attachments, malicious websites, and compromised software.
Phishing attacks are deceptive attempts to obtain sensitive information such as usernames, passwords, and credit card details by masquerading as a trustworthy entity in electronic communications. These attacks typically occur via email or fraudulent websites that mimic legitimate sites, tricking users into divulging personal information.
Ransomware is a type of malware that encrypts the victim’s data, rendering it inaccessible until a ransom is paid. This threat can cause significant downtime and financial loss, particularly for organizations that rely on continuous access to their data. Ransomware often spreads through phishing emails and malicious downloads.
Social engineering exploits human psychology to manipulate individuals into divulging confidential information. Techniques include pretexting, baiting, and tailgating. Social engineering attacks often bypass technical security measures by targeting the weakest link in the security chain: the human element.
Man-in-the-middle attacks occur when an attacker intercepts and potentially alters the communication between two parties without their knowledge. This can lead to unauthorized access to sensitive information, such as login credentials and financial data. Such attacks often take place over unsecured Wi-Fi networks.
Insider threats involve individuals within an organization who intentionally or unintentionally compromise security. These threats can be particularly damaging, as insiders often have legitimate access to sensitive information. Insider threats can arise from disgruntled employees, negligent behavior, or inadequate security policies.
By recognizing these common threats, individuals and organizations can take proactive steps to enhance their information security and privacy measures, reducing the risk of data breaches and other cyber incidents.
The Impact of Data Breaches
Data breaches have emerged as a formidable threat in the digital age, leaving a trail of devastation in their wake. The repercussions of these incidents extend far beyond immediate financial loss, permeating every layer of society. For individuals, data breaches often result in the compromise of sensitive personal information, such as social security numbers, credit card details, and private communications. This can lead to identity theft, financial fraud, and a prolonged struggle to restore personal credit and privacy. The emotional toll on victims, who often feel violated and vulnerable, is profound and long-lasting.
Businesses, regardless of their size, also suffer immensely from data breaches. Financially, the costs can be staggering, encompassing direct losses, fines, and the expense of mitigating the breach’s impact. For instance, the 2017 Equifax breach, which exposed the personal data of 147 million people, resulted in a settlement of up to $700 million. Beyond monetary losses, companies face significant reputational damage. Trust, once lost, is hard to regain, and customers may turn to competitors, leading to long-term revenue decline. Legal repercussions add another layer of complexity, as businesses may face lawsuits and stricter regulatory scrutiny, further straining resources.
The societal implications of data breaches are equally concerning. As incidents become more frequent and severe, public trust in digital systems erodes. People grow wary of sharing information online, which can stifle innovation and the adoption of new technologies. Moreover, data breaches can compromise national security, especially when sensitive government data is involved. The 2015 breach of the U.S. Office of Personnel Management, which exposed the records of 21.5 million individuals, highlighted the potential for such incidents to have far-reaching national security implications.
The long-term consequences of data breaches are a stark reminder of the ongoing challenges in ensuring information security and privacy on the internet. Victims often face years of monitoring and protecting their personal data, with the specter of further exploitation always looming. For businesses and society, the imperative to bolster cybersecurity measures has never been more urgent, requiring a concerted effort to stay ahead of increasingly sophisticated cyber threats.
Best Practices for Enhancing Information Security
Ensuring robust information security is critical in today’s digital landscape. One of the foundational steps is the use of strong, unique passwords for each of your accounts. Strong passwords typically include a mix of letters, numbers, and special characters, making them harder to crack. Utilizing a reputable password manager can also aid in the creation and storage of these complex passwords, enhancing your overall security posture.
In addition to strong passwords, enabling two-factor authentication (2FA) adds an extra layer of security. 2FA requires users to provide two forms of identification before gaining access to an account, typically something they know (a password) and something they have (such as a mobile device). This significantly reduces the risk of unauthorized access, even if passwords are compromised.
Regularly updating software is another critical practice. Software updates often contain patches for security vulnerabilities that have been discovered. By keeping your operating systems, applications, and antivirus programs up-to-date, you minimize the risk of exploitation by cybercriminals. Many systems offer automatic updates, which can ensure you never miss an important patch.
Employing firewalls and antivirus programs is also essential. Firewalls act as a barrier between your internal network and external threats, monitoring and controlling incoming and outgoing network traffic. Meanwhile, antivirus programs detect and remove malicious software, safeguarding your systems from potential harm. Regular scans and real-time protection features are crucial for maintaining security.
Vigilance about suspicious activities cannot be overstated. This involves being cautious of unsolicited emails, links, and attachments, which could be phishing attempts. Educating yourself and staying informed about the latest security threats is vital. Cybersecurity is an ever-evolving field, and awareness of new tactics used by cybercriminals can help you stay a step ahead.
In conclusion, by adopting these best practices—using strong, unique passwords, enabling two-factor authentication, regularly updating software, and employing firewalls and antivirus programs—you can significantly enhance your information security. Remaining vigilant and informed will further bolster your defenses in an increasingly interconnected world.
Protecting Personal Privacy Online
In today’s interconnected world, maintaining personal privacy online has become increasingly critical. One of the first steps is to manage privacy settings on social media platforms. Each platform provides various privacy options, which users should regularly review and adjust. Ensuring that your profile is set to private and limiting the visibility of personal information can significantly reduce exposure to potential threats.
Being cautious about the information shared online is another essential aspect of protecting privacy. Personal details like home addresses, phone numbers, and even vacation plans can be exploited by malicious actors. It’s prudent to think twice before posting and to share sensitive information only with trusted individuals.
Utilizing privacy-centric browsers and search engines can further safeguard personal data. Browsers such as Brave and search engines like DuckDuckGo are designed to minimize data tracking and enhance user privacy. These tools do not store search history or track online activities, providing a more secure browsing experience.
Tools like Virtual Private Networks (VPNs) and encrypted messaging apps also play a significant role in protecting personal information. A VPN encrypts your internet connection, masking your IP address and making it difficult for outsiders to monitor your online activities. Similarly, encrypted messaging apps like Signal ensure that messages remain confidential, accessible only to the intended recipients.
By leveraging these strategies and tools, individuals can take control of their digital footprint and enhance their online privacy. Regularly updating privacy settings, being mindful of the information shared, and using privacy-focused technologies are practical steps toward safeguarding personal data in the digital age.
The Role of Legislation and Regulation
In the realm of information security and privacy, legislation and regulation play a pivotal role in safeguarding personal data and ensuring that both businesses and consumers adhere to established standards. One of the most significant legal frameworks in this context is the General Data Protection Regulation (GDPR), introduced by the European Union. The GDPR sets stringent guidelines for data handling, mandating that organizations obtain explicit consent from individuals before collecting their data, ensure data accuracy, and implement robust security measures to protect against breaches. Non-compliance can result in hefty fines, emphasizing the importance of adherence.
Similarly, the California Consumer Privacy Act (CCPA) represents a landmark regulation in the United States. The CCPA grants California residents extensive rights over their personal information, including the right to know what data is being collected, the right to request deletion of their data, and the right to opt out of the sale of their personal information. This legislation underscores the growing recognition of consumer privacy rights and compels businesses to be more transparent and accountable in their data practices.
Beyond GDPR and CCPA, numerous other laws and regulations worldwide contribute to the tapestry of information security and privacy protection. For instance, the Health Insurance Portability and Accountability Act (HIPAA) in the United States specifically addresses the security and privacy of health information. Meanwhile, the Personal Information Protection and Electronic Documents Act (PIPEDA) in Canada governs how private sector organizations collect, use, and disclose personal information in the course of commercial activities.
For businesses, compliance with these regulations is not merely a legal obligation but also a critical component of fostering trust and credibility with consumers. Adhering to stringent data protection standards helps mitigate the risk of cyber threats and data breaches, thereby enhancing the overall security landscape. For consumers, these regulations provide a layer of assurance that their personal information is being handled responsibly and with respect for their privacy rights. Ultimately, a well-regulated environment is essential for maintaining the integrity and security of information in our increasingly digital world.
The Future of Information Security and Privacy
As we look to the future, the landscape of information security and privacy is poised for significant transformation, driven by emerging technologies and evolving threats. One of the most promising advancements is the integration of artificial intelligence (AI) in cybersecurity. AI can enhance threat detection by analyzing vast amounts of data at unprecedented speeds, identifying patterns, and predicting potential breaches before they occur. This proactive approach has the potential to revolutionize how we defend against cyber threats.
Blockchain technology also holds substantial promise for improving information security and privacy. Its decentralized nature ensures that data is distributed across multiple nodes, making it exceedingly difficult for malicious actors to compromise the system. Moreover, blockchain’s immutable ledger provides a transparent and tamper-proof record of transactions, which can be invaluable in verifying the integrity of data and preventing unauthorized access.
Quantum computing, though still in its nascent stages, is another technology that could dramatically alter the cybersecurity landscape. Quantum computers have the potential to solve complex problems at speeds unattainable by classical computers, which could both enhance encryption methods and pose new challenges. While quantum encryption offers near-impenetrable security, the same technology could also be used to break existing cryptographic algorithms, necessitating the development of quantum-resistant encryption techniques.
In addition to technological advancements, increasing awareness and proactive measures are essential in shaping a more secure and private digital future. Cyber hygiene practices, such as regular software updates, strong password policies, and the use of multi-factor authentication, play a crucial role in safeguarding personal and organizational data. Furthermore, fostering a culture of cybersecurity awareness through education and training can empower individuals to recognize and respond to potential threats effectively.
As we navigate this rapidly evolving digital landscape, it is imperative that we stay informed and vigilant. By leveraging emerging technologies and adopting proactive measures, we can collectively contribute to a safer and more private internet. Let us take an active role in protecting our information and ensuring the security and privacy of our digital lives.
发表回复